-
Get Cloud GPU Server - Register Now!
Toggle navigation

The first known computer attack dates back to as early as the first computer itself. Now that the internet is the buzzword, these, attacks are becoming increasingly common, and more than 78% devices, in some form, have had an online attack before.
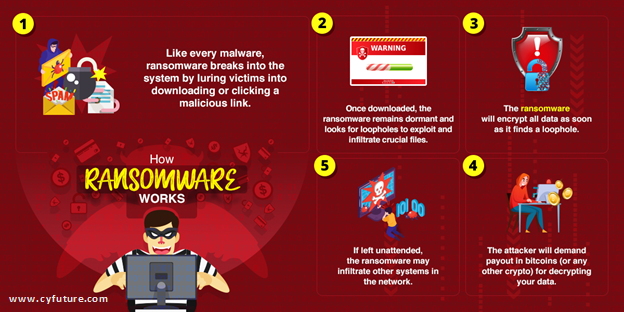
Cyberattacks, the epithet to all computer attacks, is touted to be over a dozen types; malware attack, phishing, adware, BSoD, DDoS, to name some, however none seems as frightening as the ransomware. Ransomware, to be precise, is an old player that had, at one point, lost the charm and died has now revitalized somehow, capitalizing on the post-covid market.
Ransomware attacks have more than doubled this year and were up 72% in 2020 when Covid-19 hit most nations. Cyber attackers have rolled up their sleeves, launching attacks every now and then, under the pretext of authorities battling war against coronavirus. Before this year could be any more dreadful due to sudden coronavirus surge, 77 new ransomware campaigns were successfully pulled, more than 90% of this on healthcare companies. The healthcare industry, for some reason, seems cyber attackers’ new rendezvous.
Handing over the ransom does not guarantee that your data will get restored, and only encourage attackers to continue extorting money. Infact, by paying, you are indirectly funding criminals to help them thrive on their illicit practices of blackmailing and extortion.
Vulnerable once, vulnerable ever after
According to studies, 99% of organizations that paid ransoms in 2020 received a working decrypting tool but never fully recovered 100% of their data except in 29% cases. 60% of these organizations were attacked again, and more than 85% of them again paid ransoms. In 30% of these cases, no data was restored at all, and the organizations reported total loss. As a token of insurance, attackers retain the most crucial of files and data with them for potential payoffs in the future.
Successful attacks are often the result of months of reconnaissance and social engineering. The attackers closely observe and monitor their victims’ search behavior and slip in the malware under the pretext of an email based on victims’ online interests.
As the internet becomes easily available to the masses, these criminals are eyeing a much bigger market, with multiple times the scope of launching successful campaigns. This can be corroborated by the fact that in 2015, businesses around the world paid a total $325 million in ransoms online, and until when this article was written, tween 2015 and 2021, the same is expected to surge 57 times. Setbacks due to weak cybersecurity is expected to reach 6 trillion dollars by 2021, which, until 2015, stood at a meagre $3 trillion markdown.
Hackers usually leave a calling card on your website, claiming responsibility for the attack. “The card is crucial because the hackers want you to know when and how much money should you be wiring. But for us, it helps us identify the attack method, its ransomware, and later the group likely to be involved. Once we’ve identified the ransomware, a google search gives us its decrypting tool or algorithm, as the case may be. In more than 70% cases, people can restore their content with a simple Google search but choose not to tinker with their website anymore in panic”, says one of Cyfuture’s security experts.
Rather than paying upfront, notify your local law enforcement agency that you have been hit. In half the cases in last year’s audit, the law enforcement had come up with a solution and protected interests of the vested interest groups.
India’s cybersecurity efforts constitute a meagre 1.2% of the global market that stands at whopping USD 156.24 billion. This is particularly alarming since the subcontinent is the second most attacked country in Asia pacific. Meanwhile, in other countries, efforts to curb attacks have burgeoned at tremendous 14.5% CAFR, with South Korea leading at the front line with its cavalry.
The unprecedented rate at which the internet and devices are growing in the subcontinent and around the world presents unprecedented challenges. Cyber attackers attack just about anyone they see are susceptible to extortion, especially corporates and startups. Oftentimes, attacks on enterprises are planned with even more sophisticated ransomware, narrowing down the chances of escape as had happened in 5% cases last year.
Antivirus and IT security services may look like unnecessary expenses but safeguard you from the unfortunate. Some providers even cover insurance so you are compensated for any data loss that takes places during the tenure of their service. Choosing a good host is just as important but what’s more important is that your IT security and hosting provider work in sync, which is often not the case.
Cyfuture, on the other hand, is both a security service provider and Tier-III compliant host, so you get two services in one package, and that not only saves money but also ensures better protection with a two-way firewall. This means that both incoming and outgoing traffic from your website is monitored for legitimacy and encrypted throughout across the entire connection span. All email links are filtered and checked for phishing using sophisticated and efficacious algorithms to ensure only trustworthy and business-related emails can get through. We’ll help you build a safer and more deployable IT ecosystem while taking responsibility of anything auxiliary.