-
Get Cloud GPU Server - Register Now!
Toggle navigation

Contrary to what many of you might think, the terms Bitcoin and Blockchain are not synonymous. Block chain is the underlying technology which has made Bitcoin possible. Following the success of Bitcoin and other cryptocurrencies, new applications of Blockchain technology are being discovered in areas ranging from real estate, food quality control to identity verification and even electronic voting.
Today, over 5400 merchants worldwide accept Bitcoin as a legal tender. Several major companies including Microsoft, PayPal, Shopify, Expedia and Overstock.com accept Bitcoin as a viable method of payment. In words of Tesla CEO Elon Musk:
“Bitcoin is quite brilliant. Paper money is going away in the future, that is for sure. Crypto is a better way to transfer values than a piece of paper.”
It all began when the world was reeling under global financial crisis of 2008. A developer, or group of developers under the pseudonym ‘Satoshi Nakamoto’ who apparently had been working on the Blockchain technology since early 2007, published a white paper on a ‘peer-to-peer network’ that could work autonomously without a central authority.

In January 2009, Nakamoto released the first Bitcoin software that launched the first units of Bitcoin cryptocurrency.
As more cryptocurrencies came into existence, Blockchain gained the attention of industry experts; they realized the technology could be a game-changer.

Over the past few years, Blockchain technology has found applications in an array of industries, with most such applications still in the testing stages.
Before we delve deep into understanding the nuances of Blockchain, it would be good to know certain key features of this technology:
Cryptographic hashing lies at the core of Blockchain technology. It is the feature that makes a Blockchain immutable.
Hashing involves taking an input string of any length and producing an output string (hash) of a fixed length.
For example:
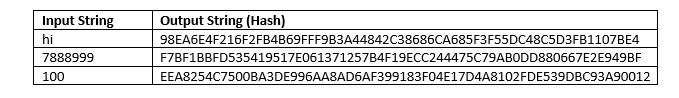
Even a miniscule change in input changes the output hash completely. Similar inputs, therefore, do not have similar outputs. For example, the hash outputs of 100202033 and 100202034 will be completely different from each other.
This property makes it impossible for anyone to guess the input by looking at output.
Obviously, two different inputs can never have the same hash output.
In any Blockchain, every block contains hash of the data in the previous block. For example, if a block chain has 500 blocks, 500th block will have hash of the 499th block, it will have a hash value of 498th block and so on.
This single property makes a Blockchain incredibly reliable.
Consider a situation where a hacker attacks block 4 in a chain. We know that even a slight change in input data changes the hash completely, so any change in block 4 will change its hash. Since all blocks have hash of the previous block, block 5 data and hash will change. This, in turn, will change the data and hash of all subsequent blocks in the chain.
The Blockchain network will notice this change immediately and reject it. That is why a Blockchain is considered immutable.
Public Key Cryptography is a system which uses a pair of keys: a public key and a private key. Every public key has a corresponding private key. The public key can be known to many, but the private key should be known to its owner only.
In a Blockchain, public-private key combination is used to encrypt and later on decrypt messages transmitted across the network. A public key can be considered equivalent to an email address and private key a password to access any mail sent to that email address.
For example, Mary wants to send a message to Jack over the Blockchain network. Mary will use her public and private key and Jack’s public key to encrypt the message.
The message will be forwarded to Jack. If a third party intercepts the message, all they will see is a string of random numbers and letters. Jack will later on use his private key to decrypt the message.
It is impossible to guess the private key using the public key. A user can, therefore, send his public key to anyone on the Blockchain network and be assured that his private key will not be stolen.
A Blockchain consists of blocks of transactions. These blocks are stored on nodes. A node can be a computer, laptop or a bigger server. All the nodes in the Blockchain remain connected to each other and constantly exchange the latest Blockchain data with one another. As a result, all the nodes in any network remain updated with respect to any changes in the network.
Every node has a copy of the transaction history of the Blockchain. No node ‘owns’ the network.
When a miner tries adding a new block of transactions to the Blockchain, it is broadcast to all the nodes on the network. Nodes can accept or reject a block depending on validity of transactions in the block. On accepting a new block in the Blockchain, nodes save it over the older blocks they have already stored.
Every time a transaction is initiated on the Blockchain, it is broadcast to the entire network, waiting to be picked by one or more miners in the Blockchain (miners are special nodes on Blockchain). As long as a transaction is not picked by any miner, it keeps lying in a ‘pool’ of non-validated transactions.
Miners pick up some transactions from this pool and form a block. A particular transaction can be picked up by more than one miner to be included in his block.
Before adding a transaction to his block, the miner needs to check if the transaction is eligible for execution based on history of the Blockchain. If, according to transactional history of the Blockchain, the sender’s wallet has adequate balance, then the transaction is eligible for inclusion in the block. Miners usually prefer transactions with higher transaction fees.
The block thus selected needs to be added to the Blockchain network. For this, the miner requires to generate a hash output (also called as signature) for the data present in the block.
This hash output is a 32 digit string of random letters, numbers and symbols, which depends on the input string and is therefore unique for each block of transactions. Each miner will thus work to generate a different hash output.
During mining, miners compete to generate a hash output for the block they are working on. A rule of Bitcoin Blockchain is that the hash output for the block needs to start with a certain number of zeros.
Since the hash output is fixed for any fixed input string, miners need to change a part of the data inside the block (called nonce) each time they guess the hash output. Each time a miner changes the nonce, the input string gets changed which leads to a different hash output.
Miners keep on changing the nonce till they get a hash output that starts with the required number of zeros. Since the process involves a lot of trial and error, mining consumes a lot of time and computational power (and hence electricity). For this reason, every node on the network does not mine theblocks.
Once a miner finds the right hash output for his block, he broadcasts the block and its hash (signature) to all other miners on the network. Other miners check if the hash attached to the block is legitimate. They do so by taking the data on the broadcasted block and hashing it to find if their hash output matches with the hash provided by the miner.
If both hash outputs match, the block gets validated and can be added to the network. The hash output provided by the miner is a proof that work has been done on the block and hence regarded as ‘Proof of Work’.
The validated block is broadcast to all other nodes in the network. The nodes accept the block and add it on the Blockchain provided transactions in the block match with transactional history of the Blockchain.
Miners are rewarded once a block that has been mined by them gets added to the network e.g. for the Bitcoin network a miner gets a certain amount of BTC for each block mined in addition to the transaction fees paid by Bitcoin users.
After a new block has been added to the network, miners need to start afresh with a new block by picking new (non-validated) transactions from the pool. They cannot continue with the older blocks there were working on earlier. This is because the block they were mining may contain one or more transactions present in the block just added to the network. This renders the older block invalid for mining.
Earlier restricted to cryptocurrencies, Blockchain technology has been well-researched and applied to every industry imaginable. Some applications are listed below:
1)Insurance claims: The insurance industry is rife with issues that hamper claim processing on time. There can be difficulty in verifying claims or understanding complex terms of contract or there may be inadequate information available. These issues affect all the stakeholders involved, be it the claimant, the insurer or any third-party.
To deal with these issues, insurance companies have begun using so-called ‘smart contracts’ in Blockchain. Under smart contracts, all the stakeholders in the claim have an access to the insurance ledger (or network) to understand policy details.
If someone makes a claim, other relevant documents such as claim forms, proof supporting the claim etc. get added to this ledger and claims are processed automatically with minimum human intervention.
Here, all the stakeholders interact directly without intervention of a third-party. Besides, every interaction gets recorded on the ledger and broadcast to all the parties involved. Smart contracts also minimize the possibility of error.
For instance, AXA has developed an insurance product Fizzy that uses Blockchain platform Ethereum to offer automatic compensation to policyholders whose flights get delayed.
When someone buys insurance on Fizzy, the transaction gets recorded on the Ethereum Blockchain. The Blockchain is linked with air traffic database provided by third-parties. When the database shows a policyholder’s flight delay by more than 2 hours, the compensation gets released automatically.
As of now, Fizzy is in the testing phase and covers direct flights between Paris’s Charles de Gaulle airport and the USA. AXA aims to partner with travel companies and airport authorities to expand the solution internationally.
2) Food traceability: Retail chains have been dealing with the issue of poor food quality for ages.
To tackle this, Blockchain platforms such as IBM Food Trust have come up, which can track food items from the time they are sown in fields to the time they are placed on shelves in retail stores.
IBM Food Trust connects all the stakeholders in the food supply chain i.e. farmers, distributors and retailers to create an immutable shared record of food data.
In September 2018, Walmart announced it would use the platform to track all the leafy vegetables brought to its shelves. The retailer has also issued a mandate which requires the suppliers of lettuce, spinach and other green leafy veggies and their partners to join the platform by September 2019. Read more.

A supply chain present on a Blockchain is more traceable, transparent and reliable. It makes all the stakeholders more accountable as they cannot afford to bring below par food items in the supply chain any longer.
Retailers can detect any infected food item early in the supply chain and prevent any epidemic outbreak. E-coli outbreak which affected many Americans last spring could have been prevented if Blockchain solution were in place. Read more.
Before IBM Food Trust came into the picture, it would require Walmart at least 7 days to trace the source of a food item. With Blockchain, the time has been reduced to just 2.2 seconds.
In fact, Walmart’s vice president of food safety, Frank Yiannas believes IBM Food Trust is equivalent to FedEx tracking food.
“You’re capturing real-time data at every point, on every single food product,” Yiannas quoted.
3) Identity verification: Identity verification typically consumes a lot of time and resources. People have to go through KYC verification from scratch every time they start something new, be it joining a new job, opening a bank account, registering a new company or applying for a driver’s license.

The new identity verification platform Civic powered by the Ethereum Blockchain is seen as a major breakthrough in this space. The user of the platform has to provide his identity details just once. Any organization or service provider wanting to verify user’s identity can cross-check all details on the Blockchain network.
The Civic ecosystem involves three interdependent entities: a user, an identity validator and an identity requestor. A user is any person who wants to register an identity on the Civic platform. He can do so by downloading the Secure Identity application.
An identity validator is an entity that validates user’s identity. The validator (with due consent from the user) can sell the user’s identity to a requestor in exchange for civic tokens. An identity requestor can be any service or organization such as a bank or an employer that wants to verify user’s identity.
Let us say a person ‘John’ wants to register on Civic. John downloads Secure Identity app. He enters all the requisite personal identity information such as name, address, date of birth, social security number, driver’s license and passport number. He secures all the information using his fingerprint. He doesn’t need to use any username and password.
Now a bank (which is a validator here), verifies the details provided by John using a standard verification procedure. The bank cross checks all information provided by John using a reliable third party (such as public records) and stores his verified identity details on the Blockchain not directly, but in form of hashes. This makes all the information highly secure.
John now applies for an insurance policy. The insurance company (an identity requestor here) communicates with John and submits a data request to the bank. The bank with John’s consent sells ‘access rights’ to the insurance company. The company verifies John’s identity and both John and the bank receive tokens.
While Civic and other such platforms may still be in the nascent stage, they promise to considerably reduce the time and effort needed for identity verification. Besides, they assure users of the security of their personal information.
4) Cross-border transactions: While the financial world has succeeded in bringing everything online, cross-border transactions are still considered a hassle by many.

The traditional network for cross-border payments suffers on several counts. A cross-border transaction takes anywhere between three to five working days to complete.
A single transaction involves many parties, each party levies a fee on the transaction amount. For high transaction volumes fees may be less; but for lower volumes fees can be up to 10% of the transaction amount. Besides, it is very difficult to keep track of the money while in transit. The receiver is not certain when the money will reach him.
To improve this scenario, financial institutions are teaming up with technology companies to develop Blockchain solutions that facilitate cross-border payments.
In September 2018, MasterCard teamed up with Microsoft on one such payment platform.
Blockchain platforms, when fully functional, would facilitate direct payment between the sender and the receiver and eliminate the middleman. The transactions would not carry hefty charges characteristic of traditional transfer networks. Besides, cryptographic hashing would ensure that the transactions remain secure.
5) Land Registry: The current land registry space is replete with instances of corruption and inefficiency, more so in developing countries. In several cases, the land in question is disputed and the rightful owner cannot be identified.
Sometimes, the owner is not certain if he legally owns the place even when he has all the requisite documents. Then there are cases when the buyer is not sure if the person selling the land is the rightful owner. If the buyer or the seller loses one or the other document, matters become even worse.
Using an appropriate Blockchain solution, the land registry authorities can create an immutable record of all land transactions which all parties can see at any time but can never modify. This would reduce time and cost involved in transactions and prevent any dispute.
To understand this better, consider two parties, a buyer ‘A’ and a seller ‘B’ who have negotiated the terms of sale of a land and want to register this sale with the local authorities. So, both ‘A’ and ‘B’ go to the government office where an officer registers the sale into their system, now operating on Blockchain platform.
The system records the transaction in presence of both ‘A’ and ‘B’ and processes sign-offs by both the parties. The transaction now moves to verification stage. Post verification, the system automatically transfers ownership from ‘B’ to ‘A’.
In a path-breaking move, the United Nations Development Program (UNDP) has teamed with Block chain companies to bring land registry on Ethereum Blockchain for the city of Panchkula in Haryana, India.
In another instance, UK government’s HM Land Registry has partnered with software company Methods who will use Blockchain platform to work on a project entitled, Digital Street. The project involves research and development to understand how Blockchain and smart contracts can transform the buying and selling of property in the UK. Read more.
Blockchain has been criticized for being vulnerable to attacks by hackers and other criminals. The technology, nevertheless, has enormous potential. It makes transactions more secure, more transparent and stakeholders more accountable. We hope more innovative applications of Blockchain will come up soon. In short, Blockchain is here to stay.
[…] Read: Blockchain Technology – How Is It Shaping The World Around Us? […]
[…] What are your views on Blockchain technology being used in films? Please share in the comment section below. In case you want to read more about Blockchain, click here. […]
Here I get to know some useful ideas on Blockchain technology. This technology is very advanced. This is like virtual money. I get some useful ideas here.
[…] Blockchain is touted as one of the most revolutionary technologies of the current times. It has found applications in areas ranging from insurance and food supply chain to identity verification and cross-border transactions. […]
Blockchain can be described as the world’s leading platform for digital currency. Blockchain has revolutionized the whole world and India is no exception to it. Looking at the applications of blockchain right from the finance sector to the healthcare sector, India has finally adopted blockchain technology for aiding its various ailing industries.
I read the complete article & sincerely appreciate your knowledge & writing. Blockchain is the most advanced
technology for processing transaction and there is a wide application of blockchain.
It was worth reading the article. You’ve actually put a ton of effort into writing this. Blockchain application was portrayed very beautifully and its characteristics. Hope to read more about this article.
Very well written. Appreciate your knowledge and writing style. In addition to these points, blockchain technologies are even used in space research & development. Blockchain technologies have brought revolution to this modern tech world.
The blog was absolutely fantastic| Lot of great innovative information which can be very helpful. Thanks for sharing such wonderful information.
All this information is really very helpful for all the users. Thanks for sharing such useful ideas here. This is definitely helpful for all Mac users. Keep sharing.
You have guided all the information very nicely here. This type of information is just awesome. Here I get some rare ideas. Which will be definitely helpful for other users also.
Thanks for this wonderful post, I heard block chain technology will have some impact on bitcoin and cryptocurrency, with your article got to know more about block chain technology.
Yor are guided to everyone through your knowledge
it’s really a great post. And the way you describe you about the Blockchain and its applications this makes very easy to understand for the non-technical purpose.
Nice blog| I have gained good knowledge about Blockchain.`
https://www.kellytechno.com/Hyderabad/Course/blockchain-training-in-hyderabad
This blog is very interesting and thanks for the informative content. If you need further assistance on
developing a mobile app, reach us at: http://bit.ly/2mijp4h
The implementation of blockchain technology in real life scenarios are increasing day by day. Blockchain came to existence with cryptocurrencies and is used for a secure payment system. Passport Verification is the latest application of blockchain technology.
Hi Dear,
First of all thank you so much for sharing your valuable information full article, about distributed ledger blockchain technology. At before read this article I was not clear about Blockchain technology properly now I’m reading this article. It was very good and whatever I could not understand, it got cleared here. Keep posting so that we can get more information related to Blockchain technology.
Thanks to you again.
Greate post.It was nice reading it.
Hey!, @Parul Singh. I went through your entire article which was written about blockchain technology in a good manner, Here, I get to know more information about Blockchain technology. Blockchain is one of the most advanced technologies which helps many industires to make their transactions in a well-secured manner. Thanks! for sharing with us.
Thanks for the appreciation Tim.
Thanks for the appreciation.
Thoroughly explained and rightly said, blockchain technology is truly shaping in world around us in every possible section. The most in-demand technology in the world of web.
Interesting article on blockchain applications in the real-world. Blockchain for sure is the trending & fool proof technology
Hi… These blogs offer a lot of information about Blockchain Development. Your blog is incredible, it helps a lot to understand about the Blockchain Technology. I am delighted with it. Thank you for sharing this wonderful post.
Well it’s a known fact that blockchain has changed the world so much , but still it’s majorly use limited to Cryptocurrency.
Hi… These blogs offer a lot of information about blockchain development.Your blog is incredible, it helps a lot to understand the concept of blockchain. I am delighted with it. Thank you for sharing this wonderful post.
Hello @Parul Singh Thanks for sharing such an informative article. I often check for new updates regarding, but this one is an wonderful one and have helped me to recall the blockchain related things.
Insightful article covering the blockchain from basics to complex points. Thanks for the share.
Blockchain for Marketing and How it’s work
Greetings @Parul Singh. Great article to read through. you have explained very well about blockchain technology in an understandable way to the beginners. Keep on sharing various articles on the blockchain.
hi,
thanks for sharing the information and explanation about the features of the blockchain. hope it is useful.
Thanks for sharing this information. Keep up the good work. For instant support related to the Epson Printer Error Code 0x10 please visit http://www.printercustomerservice.co/blog/epson-printer-error-code-0x10/ for the best solutions.
Thanks for sharing such an informative blog, Blockchain technology is having a huge impact on bitcoin and cryptocurrencies, with your article got to know more about blockchain.
Yes, As per your title Xamarin is the best mobile application development solution. I can say that because I am also one of the good firm Moon Technolabs – the xamarin app development company. I read your opinion and get that It’s too important for you and the firm who are delivering good cross-platform app development. Good wishes for your success and grab more and more.
Great Article Parul Singh. Very informative. Thanks for sharing such a useful post.
Such a nice article that I have come across. This completely described about the effort that blockchain technology to make the world to a next level. Thanks for sharing !!
Hi! Parul, The article you have shared has nuke and corners of the Blockchain technology and it is very useful for entrepreneurs to know the concept behind the blockchain how it will be helpful for them to inculcate in their business.
Thanks for sharing.Keep it up. What is forex
Hi! This article is very interesting and very informative about blockchain technology. Thanks for sharing.
Great Article to read. Thanks for sharing !
Make your own strategy for the best trading and blockchain is the top platform where crypto trader shares his analyses. Best damn trading article I’ve seen yet! Thank you for this, gonna give this to new traders, sums everything up perfectly! The insights about blockchain technology help sort out a lot of queries. It definitely covers all the points of How Is It Shaping.
Thanks for posting such a helpful article related to Blockchain Technology.
Blockchain technology is the greatest thing happened with us in 21 century. It’s the only way to save the value of our money safely. Bitcoin concept proved it’s existence for more than 10 years and now we could be free of global financial system made by governments.
I have read this blog and i think that this is written very well. Thanks for providing a good information.
Great post on Blockchain! Thanks for sharing.
Really Informative One!
Great Article, I learn something about the blockchain technology. Keep sharing an article like this.
Thanks for the appreciation.
Hi, great post it is! Thanks for sharing this with us.
I am totally agreed with this article and i just want say that this article is very nice and very informative article. I will make sure to be reading your blog more.
Hello; you have opened a very successful topic. That’s very good that the people getting awareness via your page.
I have been following your page for a long time and I find it really useful. I am very happy to read the text of valuable people like you. I wish you continued success. Yours truly.